In December last year Oxford University students were offered £15,000 in prize money if they could solve challenges relating to the surveillance and tracking of devices and their users.
‘Huawei welcomes a selection of top-of-the-class students to their 2021 University Challenge’, the invitations read. The company added that the technology would be used for ‘business intelligence’ and ‘security services’.
The invitation to the ‘hackathon’, as Huawei described it, was aimed at data science students, and was relayed by Oxford’s careers service just a few weeks before Christmas. When one student questioned whether it was appropriate for the careers service to be passing this on when Huawei’s technology was implicated in the repression of the Uyghurs in Xinjiang, she received a perfunctory reply. ‘We offer an impartial service,’ it said, and it was up to students whether they wanted to engage or not. It referred her to the terms and conditions of the service.
It is hard to say what was the most shocking part of the incident. The audacity of a company with close links to the Chinese Communist Party, which is barred from Britain’s 5G telecoms networks on security grounds? Or the apparent indifference of Oxford University? But it is just one example of the brazen way in which entities linked to the CCP are able to trawl for information and technology in Britain, with few questions asked.
The word Qingbao in Chinese means both ‘intelligence’ and ‘information’, and it neatly encapsulates the unique nature and breadth of a China’s vast spying system, which combines formal and informal techniques, both overt and covert, to obtain new intelligence. There is often a fine line between theft and the voluntary transfer of know-how, and China has pushed the latter to the limit. Over the years, the CCP has built a comprehensive system for spotting and acquiring foreign technologies by multiple means.
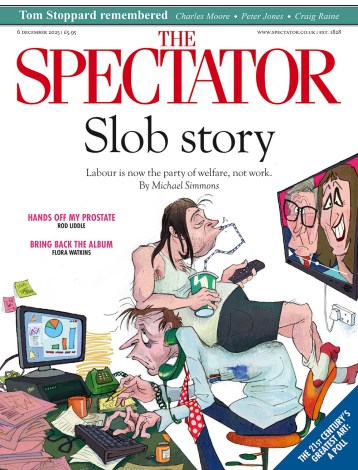
Many Chinese partners make little attempt to hide their affiliation with the CCP or military
China’s cyber spies are one face of this system, and have hacked the computers of western companies on an industrial scale. The targets closely align with the advanced technologies identified by the CCP as those in which it wants to lead the world.
In one operation I was told about while researching a book on Chinese surveillance, hackers penetrated a US oil company by infecting the online menu of a local Chinese restaurant where systems engineers ordered their takeaways. When the engineers clicked on General Tso’s chicken, they got a lot more than sweet crispy meat.
The scale of the hacking is breathtaking. America’s Office of National Counter Intelligence Executive described Chinese actors as the ‘world’s most active and persistent perpetrators of economic espionage,’ While General Keith Alexander, then head of US Cyber Command and the National Security Agency, once famously described America’s loss of intellectual property and other industrial information through cyber espionage as ‘the greatest transfer of wealth in history.’
Despite its scale, the tradecraft is often sloppy. Hackers frequently leave behind digital fingerprints, which can be traced back to China. Last year, Britain joined the US, EU, Australia and other allies in accusing Beijing of working with criminal groups to breach Microsoft’s email systems, which affected tens of thousands of companies and public sector organisations worldwide. The coordinated condemnation was unprecedented.
In its 2021 annual report Britain’s National Cyber Security Centre, which is part of GCHQ, said cyber ‘incidents’ were running at a record level, and that Covid-19 vaccine research had become a prime target for hackers. ‘China remained a highly sophisticated actor in cyberspace with increasing ambition to project its influence beyond its borders and a proven interest in the UK’s commercial secrets,’ it warned. MI5 chief Richard Moore said that China is now his organisation’s single biggest priority.
China’s principal espionage agency is the Ministry of State Security, the Guoanbu, which is responsible for foreign and counterintelligence, and ranks among the world’s largest intelligence agencies. The People’s Liberation Army has parallel organisations. Intelligence work is closely coordinated with the United Front Work Department (UFWD), which concentrates on influence operations, and which has been vastly expanded under Xi Jinping. Christine Lee, who was outed last week by MI5 as a Chinese agent, was allegedly working for the UFWD.
Where the Guoanbu has recruited conventional agents, it has tended to concentrate on people of ethnic Chinese heritage, from whom it thinks it can demand loyalty. It has been accused of using LinkedIn to trawl for potential agents, seeking to lure them to China for meetings about ‘well paid’ opportunities before recruiting them.
But conventional agents tend to have a back seat in China’s intelligence set-up for the simple reason that its informal methods have been so fruitful. This is particularly the case in higher education. It makes little sense to steal or buy, when gullible universities can be persuaded to give away sensitive information free of charge. In this way, much of China’s intelligence work is done by an informal network of academics, students or business people, who help the CCP as and when they can. This work might be at a commercial or technological level – or as with Ms Lee, it might involve the broader peddling of influence. This presents an enormous challenge to British intelligence agencies, as it falls below the bar of current espionage laws.
China has established a network of ‘dual-use’ friendship and cultural organisations. Within higher education, Confucius Institutes ostensibly teach the Chinese language, while the China Students and Scholars Association is concerned with the welfare of Chinese students, the biggest single group of foreign students at British universities. Yet both have been accused of peddling propaganda, spying on students and intimidating critics. Internationally, they have been investigated and sanctioned, but continue to be given free rein in the UK.
Another preferred method of intelligence gathering has been through joint research centres or funding research projects. Research collaborations between the UK and China increased by 115.6 per cent between 2013 and 2019. There were 15,623 such collaborations in 2019, making China Britain’s biggest research partner after the US and Germany, and the fastest growing partnership.
Many Chinese partners make little attempt to hide their affiliation with the CCP or military, and British universities have shown little curiosity or transparency about often opaque sources of funding. Cambridge University has accepted millions of pounds from the Chinese government to set up a ‘smart cities’ research centre in the city of Nanjing, which it describes as its ‘most ambitious’ Chinese collaboration to date. ‘Smart city’ tech may well improve urban lifestyles, but in Xi Jinping’s China that same technology is also enabling hitherto unseen levels of surveillance and repression.
It should be remembered that a raft of security laws in China mean that companies and researchers are required to cooperate with the state’s intelligence agencies when asked. ‘Civil-military fusion’, the obligation of researchers to share their findings with the security apparatus, has even been written into the constitution.
Late last year it was reported that China was massively expanding its ability to mine western social media, including Facebook and Twitter, for information on potential foreign targets. This seems like a chilling extension of China’s intelligence reach, but it does raise another issue – one of digestion. China’s intelligence operations have been likened to a vast vacuum cleaner, hoovering up everything and anything they can – often dubbed the ‘thousand grains of sand’ approach.
A better way of describing it is a layered system, with various degrees of formality and multiple techniques. But that still presents the challenge of making sense of the vast amounts of data generated, even with machine learning. Ultimately it is not raw data, but analyses that make workable and applicable intelligence, and the Guoanbu is not thought to have strong analytic capabilities.
There are some encouraging signs that the world is growing aware of the risks. British athletes preparing to travel to Beijing for the Winter Olympics have been offered temporary phones for use while there, out of fear that the authorities could install spyware to extract private information or track their future activity. For the same reason, Western business executives visiting China now routinely take throwaway laptops and burner phones. It is a pity that sort of vigilance is not being displayed closer to home, with Britain’s intelligence agencies seemingly in despair at the lack of awareness of potential risks in sensitive industries and research centres.





Comments